Apple iOS 18.3.1: An Urgent Security Update
On February 11, 2025, Apple released iOS 18.3.1—a rapid, emergency update aimed at patching a dangerous vulnerability that had already been exploited in real-life attacks. This isn’t a routine update with a batch of minor bug fixes; rather, it addresses a single, critical flaw that could allow a physical attacker to disable USB Restricted Mode on a locked device.
---
Understanding the Critical Vulnerability
What’s the Issue?
At the heart of the matter is a security weakness in the Accessibility feature of iOS. Tracked as CVE-2025-24200, the vulnerability allows an attacker with physical access to a device to disable USB Restricted Mode—a core safeguard designed to protect sensitive data.
Apple’s support page noted, “Apple is aware of a report that this issue may have been exploited in an extremely sophisticated attack against specific targeted individuals.” The fact that the details are being tightly controlled only underlines the severity of the issue.
How Does USB Restricted Mode Work?
Introduced with iOS 11.4.1, USB Restricted Mode was designed to ensure that when an iPhone or iPad is locked, its USB port can only be used for charging. This prevents data transfer via USB accessories—stopping potential attackers from connecting rogue devices that might try to extract sensitive information. In simple terms, it creates a barrier between your locked device and any peripheral that could misuse the connection.
Security researcher Josh Long explains that without this safeguard, even sophisticated tools (such as those once limited to law enforcement) might be repurposed by malicious actors if they physically access the device.
---
Behind the Patch: How the Vulnerability Was Uncovered
The Role of Cybersecurity Researchers
The vulnerability wasn’t discovered in a vacuum. Bill Marczak of The Citizen Lab—a renowned research group at The University of Toronto’s Munk School—reported the flaw. The Citizen Lab’s involvement in uncovering the issue highlights the persistent and advanced nature of digital espionage and surveillance methods in today’s interconnected world.
The Nature of the Attack
While the vulnerability is technically complex, its impact is straightforward: it potentially opens the door to attacks against high-profile individuals. Journalists, dissidents, business leaders, and government officials—people who are likely to be targeted by sophisticated adversaries—are the primary risk group. The update, therefore, isn’t just a routine patch but a targeted measure to protect those who might be in the crosshairs of advanced physical attacks.
---
Who’s Affected and What You Should Do
Affected Devices
Apple’s rollout of iOS 18.3.1 is not universal across all older devices. The patch is available for:
iPhone XS and later models
iPad Pro 13-inch, iPad Pro 12.9-inch (3rd generation and later)
iPad Pro 11-inch (1st generation and later).
iPad Air (3rd generation and later)
iPad (7th generation and later)
iPad mini (5th generation and later)
For devices not receiving this update, it is likely that the vulnerability does not affect them. However, for anyone using a supported device, this update is essential.
How to Update
If you have one of the above devices, follow these steps:
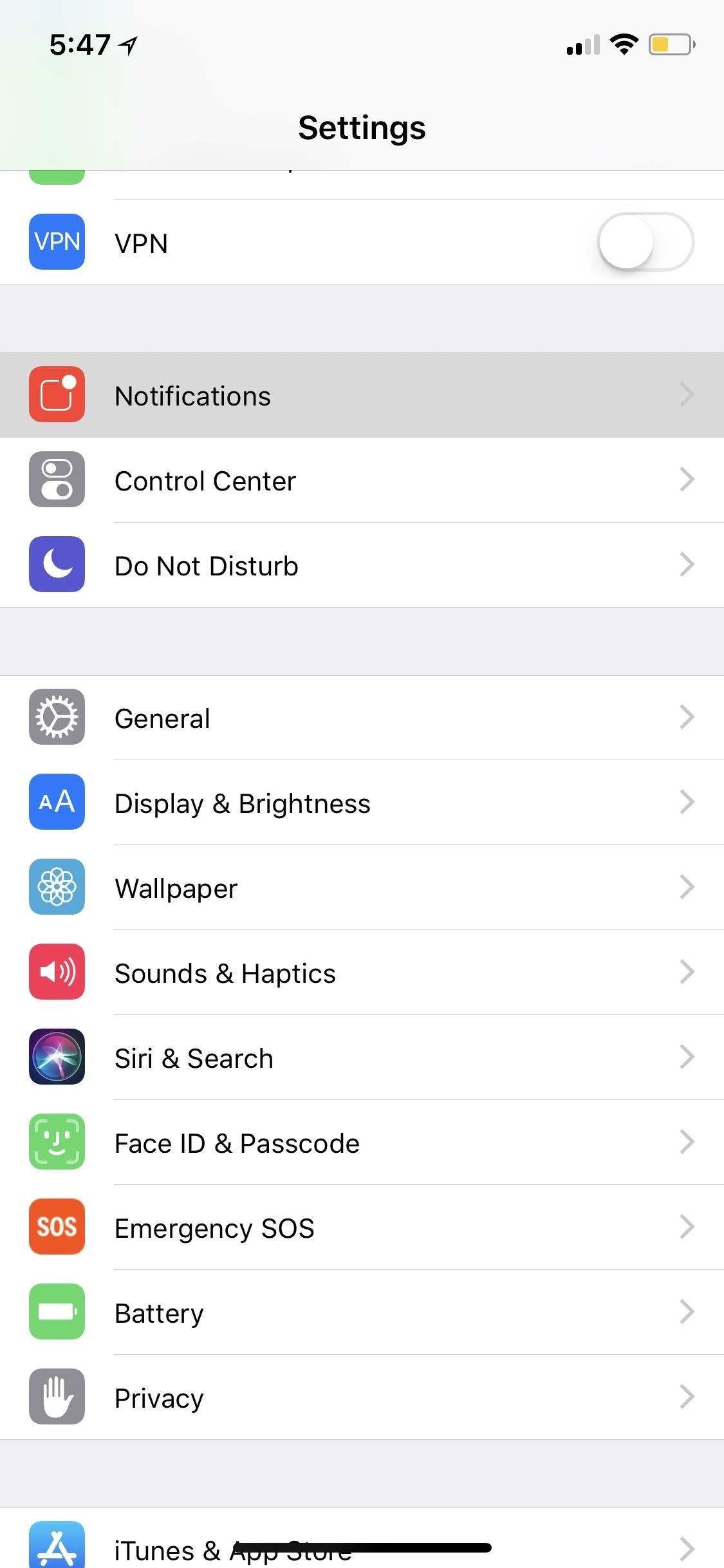
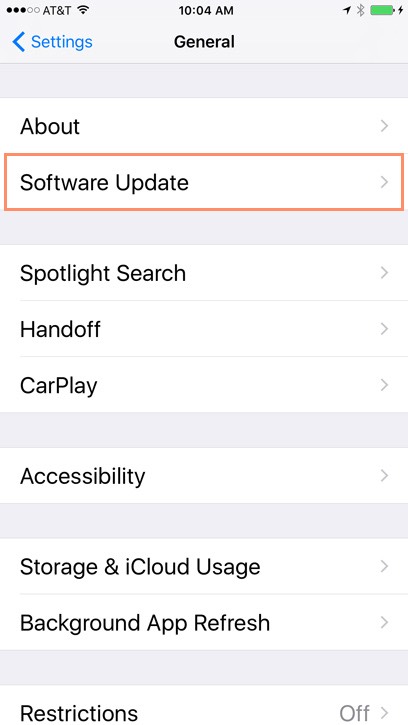
1. Open the Settings app.
2. Tap on General.
3. Select Software Update.
4. Follow the on-screen instructions to download and install iOS 18.3.1.
Apple’s guidance is clear: if your device is affected, update immediately. Waiting could leave you vulnerable to sophisticated attacks exploiting this flaw.
---
Why This Update Matters
Defending Against Sophisticated Attacks
In today’s digital age, where both physical and digital security are increasingly interwoven, a seemingly small vulnerability can have significant consequences. The potential exploitation of this flaw underscores a broader trend: attackers are not only refining their software exploits but are also turning to physical attack vectors. By compromising USB Restricted Mode, an attacker can bypass one of the last lines of defense on a locked device.
Reaffirming Trust in Security Measures
Apple’s rapid release of iOS 18.3.1 sends a powerful message about its commitment to user security. Even though the details of the vulnerability are scarce—part of a deliberate effort to prevent further exploitation—the company’s swift action helps protect both high-profile targets and everyday users who might otherwise be at risk.
---
Conclusion
The release of iOS 18.3.1 is a stark reminder of the evolving landscape of cybersecurity. With vulnerabilities like CVE-2025-24200, attackers are increasingly capable of leveraging physical access in ways that bypass traditional security measures. For anyone using a supported Apple device, updating to iOS 18.3.1 isn’t just a recommendation—it’s a critical step to ensure that your personal and professional data remains secure.
Staying updated with the latest security patches is one of the simplest yet most effective ways to guard against sophisticated cyberattacks. In the fast-moving world of digital security, vigilance and prompt action remain your best defense.
---
By breaking down the technical aspects of the vulnerability, understanding the importance of USB Restricted Mode, and emphasizing the need for immediate action, this article aims to provide a comprehensive overview of why iOS 18.3.1 i
s not just another update, but a vital shield in the ongoing battle against targeted cyber threats.












Comments
Post a Comment